GOOGLE'S QUANTUM AI team has a peculiar problem: it has figured out how to describe the precise shape of a weapon it has not yet built, and it needs the world to believe the blueprints are real without actually handing them over. In a whitepaper published on March 31, the team revealed that breaking the elliptic curve cryptography underpinning most blockchain systems could require roughly 20 times fewer quantum resources than the field's previous best estimates — fewer than 500,000 physical qubits, executable in minutes. To prove the claim without arming bad actors, the researchers did something no quantum lab has done before: they published a zero-knowledge proof, a cryptographic construction that lets anyone verify the result while revealing none of the underlying attack circuits.
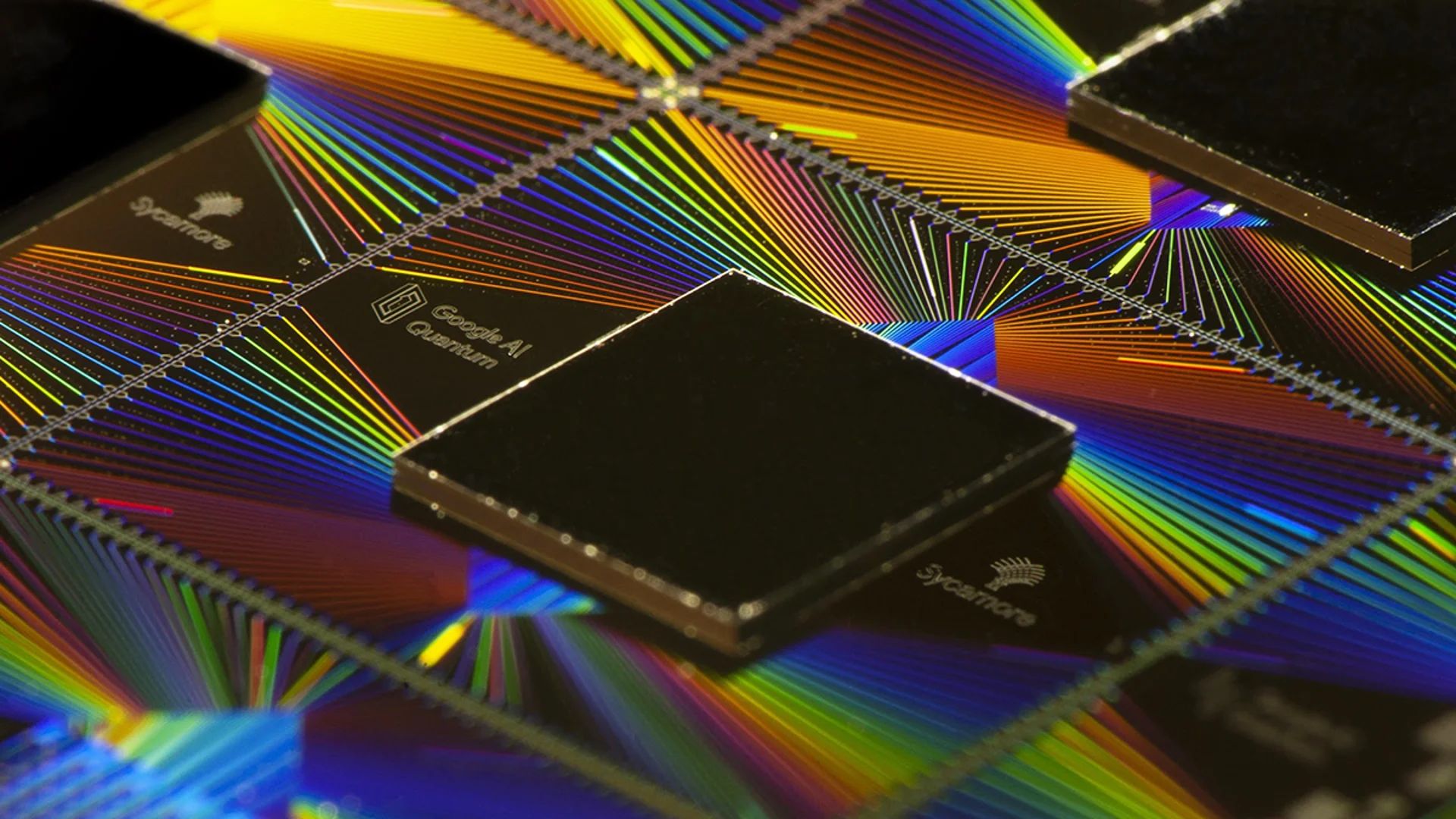
The numbers are sobering. Google compiled two quantum circuits implementing Shor's algorithm against the 256-bit elliptic curve problem (see Chart): one using fewer than 1,200 logical qubits and 90 million Toffoli gates, another using fewer than 1,450 logical qubits and 70 million gates. Under standard hardware assumptions consistent with Google's own superconducting architecture, either circuit could run on a machine with under half a million physical qubits. For context, Google's current flagship processor, the Willow chip unveiled in late 2024, has 105 qubits — a gap of roughly 5,000x. That gap is shrinking. Google has set a 2029 deadline for its own migration to post-quantum cryptography, a timeline that Dragonfly Capital managing partner Haseeb Qureshi called "serious," warning that every blockchain needs a transition plan immediately. The paper's co-authors include Ethereum Foundation researcher Justin Drake and Stanford cryptographer Dan Boneh, lending the findings unusual cross-institutional weight.

Proof of concept, proof of worry
Yet the most interesting element of Google's paper may not be the qubit estimates at all — it may be the disclosure model. Vulnerability disclosure in computer security has well-established norms: find a bug, notify the vendor, embargo details, publish after a fix ships. Google's own Project Zero operates on a strict 90-day deadline. But cryptocurrency has no vendor to call. Blockchains are decentralized; there is no patch Tuesday, no single entity that can roll out an update across millions of wallets. And the asset class has an additional fragility that conventional software does not: its value depends as much on collective confidence as on underlying cryptographic security. As Google's researchers noted, even unsubstantiated claims about quantum capabilities can constitute an attack on a system whose worth is tethered to perceived invulnerability. Fear, uncertainty, and doubt — FUD, in crypto parlance — is itself a threat vector.
This is what makes the zero-knowledge proof so clever. By allowing independent verification without leaking the circuit design, Google threads a needle between two bad outcomes: staying silent while the threat grows, or publishing a roadmap that accelerates it. The approach borrows the vocabulary of blockchain itself (zero-knowledge proofs are a staple of privacy-preserving protocols like Zcash) and turns it back on the ecosystem as a warning.
The practical implications are considerable, albeit unevenly distributed. According to Google's analysis, approximately 6.9 million bitcoin — roughly a third of total supply — sit in wallets where public keys have already been exposed on-chain, whether through early address formats or the Taproot upgrade that Bitcoin adopted to improve transaction efficiency. Taproot, ironically, makes public keys visible by default in many spending conditions, widening the very attack surface that quantum computing threatens. A sufficiently fast quantum machine could intercept a Bitcoin transaction mid-flight; Google models suggest roughly a 41 percent chance of completing the attack within nine minutes, just under Bitcoin's typical ten-minute block confirmation time. Ethereum faces its own vulnerabilities across at least five vectors — wallets, smart contracts, staking infrastructure, layer-two networks, and data availability mechanisms — with combined exposure that one analysis put above $100 billion.
The cryptocurrency market, which briefly surpassed $4 trillion earlier this month before retreating to around $2.4 trillion, is not treating this as an existential crisis. Post-quantum cryptographic standards exist; NIST finalized several in recent years, and experimental PQC deployments are already running on some blockchains. The Ethereum Foundation launched a post-quantum research portal backed by eight years of work, with test networks shipping weekly and a multi-fork upgrade roadmap targeting quantum-resistant cryptography by 2029. The tools, in other words, are available. The question is whether a decentralized ecosystem can coordinate a migration at the speed the timeline now demands — and what happens to the estimated millions of dormant wallets, holding billions in value, whose owners cannot or will not upgrade.
Google's Willow chip currently sits at 105 qubits; 500,000 is a long way off. But in 2012, the consensus estimate for cracking 2048-bit RSA was a billion physical qubits. By 2024, that had fallen to a million noisy ones. The direction of travel is monotonic, even if the arrival date is not. The crypto industry has, at most, a few years to upgrade its locks — and Google, to its credit, has found a way to ring the alarm without handing out lockpicks. ■
For more, join 75,000 subscribers getting tech's favorite brief here
