Google proved it can pick crypto's lock
But it didn't publish the key
GOOGLE'S QUANTUM AI team has a peculiar problem: it has figured out how to describe the precise shape of a weapon it has not yet built, and it needs the world to believe the blueprints are real without actually handing them over. In a whitepaper published on March 31, the team revealed that breaking the elliptic curve cryptography underpinning most blockchain systems could require roughly 20 times fewer quantum resources than the field's previous best estimates — fewer than 500,000 physical qubits, executable in minutes. To prove the claim without arming bad actors, the researchers did something no quantum lab has done before: they published a zero-knowledge proof, a cryptographic construction that lets anyone verify the result while revealing none of the underlying attack circuits.
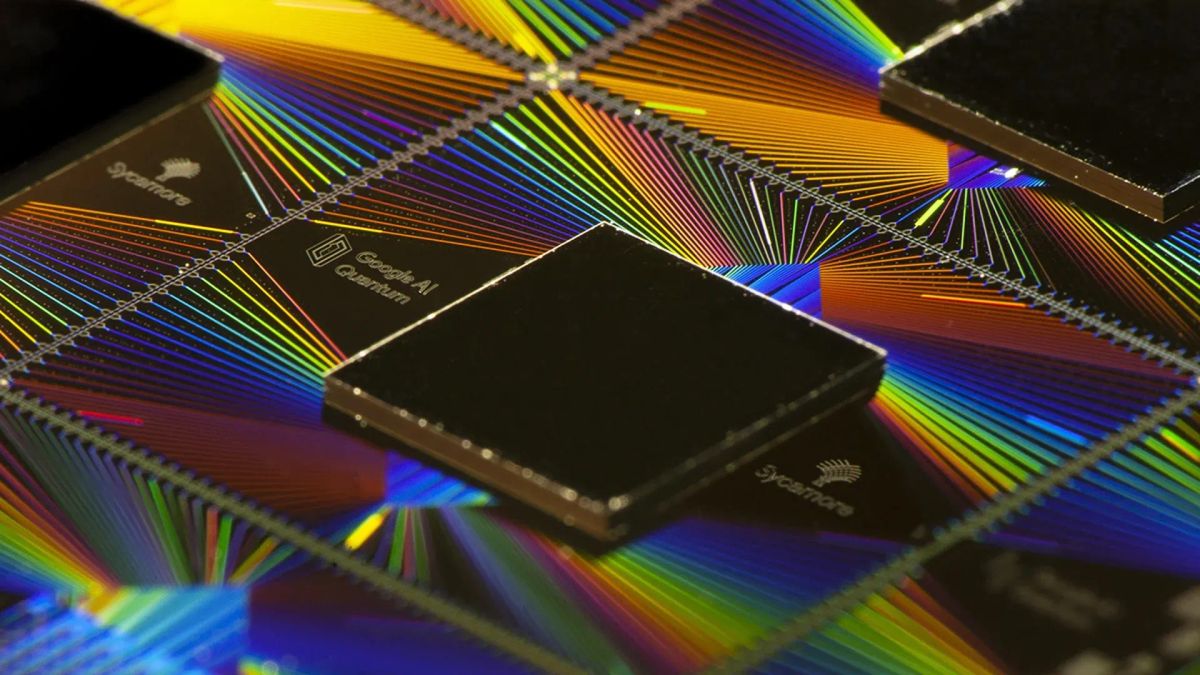
The numbers are sobering. Google compiled two quantum circuits implementing Shor's algorithm against the 256-bit elliptic curve problem (see Chart): one using fewer than 1,200 logical qubits and 90 million Toffoli gates, another using fewer than 1,450 logical qubits and 70 million gates. Under standard hardware assumptions consistent with Google's own superconducting architecture, either circuit could run on a machine with under half a million physical qubits. For context, Google's current flagship processor, the Willow chip unveiled in late 2024, has 105 qubits — a gap of roughly 5,000x. That gap is shrinking. Google has set a 2029 deadline for its own migration to post-quantum cryptography, a timeline that Dragonfly Capital managing partner Haseeb Qureshi called "serious," warning that every blockchain needs a transition plan immediately. The paper's co-authors include Ethereum Foundation researcher Justin Drake and Stanford cryptographer Dan Boneh, lending the findings unusual cross-institutional weight.
Proof of concept, proof of worry

Yet the most interesting element of Google's paper may not be the qubit estimates at all — it may be the disclosure model. Vulnerability disclosure in computer security has well-established norms: find a bug, notify the vendor, embargo details, publish after a fix ships. Google's own Project Zero operates on a strict 90-day deadline. But cryptocurrency has no vendor to call. Blockchains are decentralized; there is no patch Tuesday, no single entity that can roll out an update across millions of wallets. And the asset class has an additional fragility that conventional software does not: its value depends as much on collective confidence as on underlying cryptographic security. As Google's researchers noted, even unsubstantiated claims about quantum capabilities can constitute an attack on a system whose worth is tethered to perceived invulnerability. Fear, uncertainty, and doubt — FUD, in crypto parlance — is itself a threat vector.
This article is for Vector members. Start a 7-day free trial to keep reading.
Start your free trial


